What's on your network?
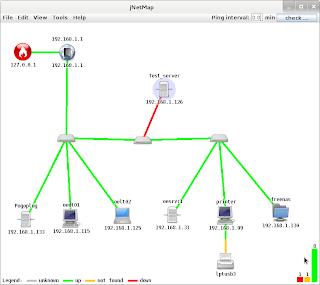
Ever wanted to know what is on your network graphically? There is a program that works on most platforms that support the java gui. Your best chance to document your home network. The program is jNetMap. The java version seems a lot more stable now. You can find it on sourceforge.net You can start up the the program very easily from the command line with (if you have java installed): $ java -jar jNetMap.jar or C:\> java -jar jNetMap.jar The instructable: http://www.instructables.com/id/Map-your-network-visually/ has more information also. Once you run the software on your network and scan for devices, you can get a roadmap of what is there. What is really neat about it is, you can see what devices are up or down on the network and it makes trouble shooting easier. You can also see rogue devices on the network also that need to be investigated. You can use the mouse to move all the icons around to make the map more readable. You can even add notes to define wher...




